by admin | May 8, 2024 | Network Security
EnlargeGetty After reversing its positioning on remote work, Dell is reportedly implementing new tracking techniques on May 13 to ensure its workers are following the company’s return-to-office (RTO) policy, The Register reported today, citing anonymous sources....

by admin | May 8, 2024 | Network Security
Enlarge / In 1984, the year 2000 was so promising, students made entire games promising to take you there. Radio Student Software is almost impossibly easy to download, distribute, and access compared to 40 years ago. Everything is bigger, faster, and more flexible,...

by admin | May 8, 2024 | Network Security
Enlarge / A still image of a robotic quadruped armed with a remote weapons system, captured from a video provided by Onyx Industries.Onyx Industries The United States Marine Forces Special Operations Command (MARSOC) is currently evaluating a new generation of robotic...
by admin | May 8, 2024 | Network Security
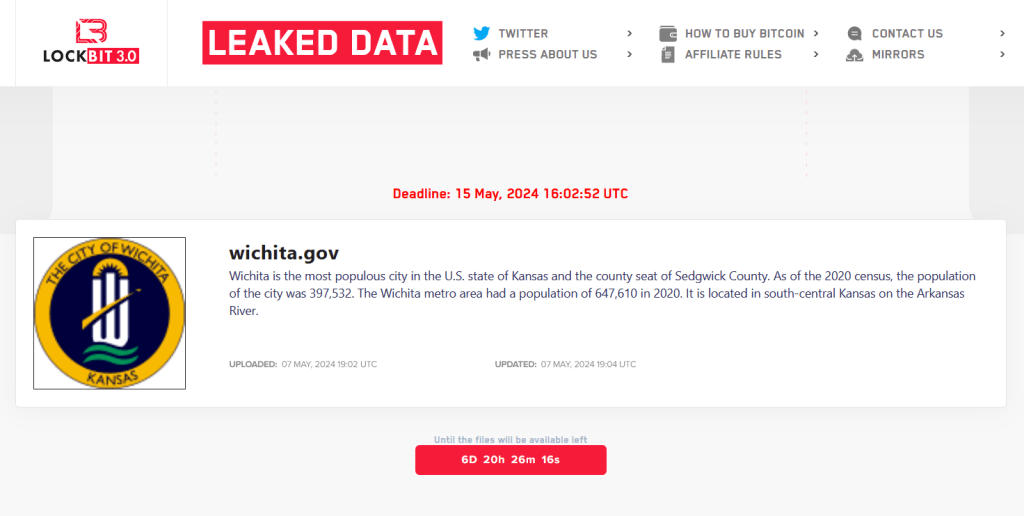
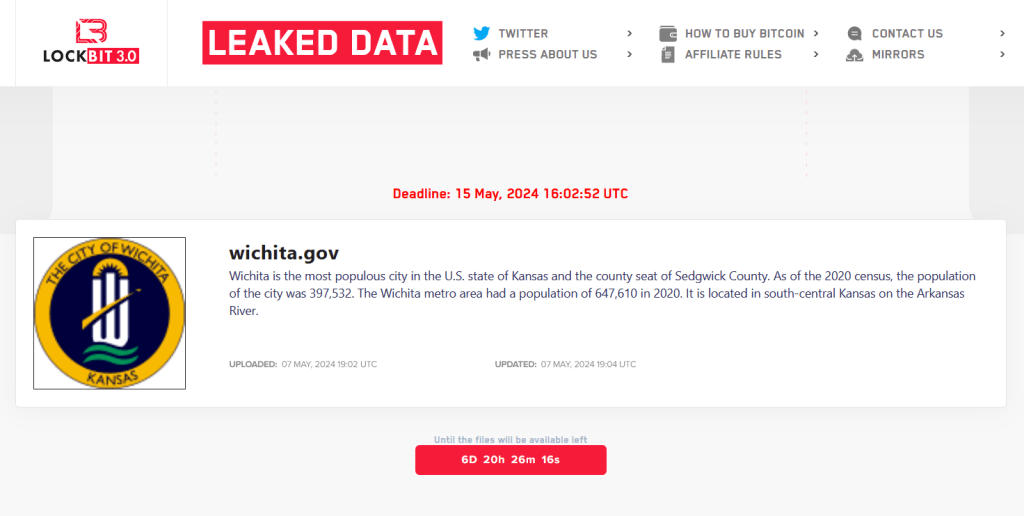
LockBit gang claimed responsibility for the attack on City of Wichita Pierluigi Paganini May 08, 2024 The LockBit ransomware group has added the City of Wichita to its Tor leak site and threatened to publish stolen data. Last week, the City of Wichita, Kansas, was the...

by admin | May 8, 2024 | Network Security
Enlarge / Prediction of the structure of a coronavirus Spike protein from a virus that causes the common cold.Google DeepMind Most of the activities that go on inside cells—the activities that keep us living, breathing, thinking animals—are handled by proteins. They...

by admin | May 8, 2024 | Network Security
Explosion in Threat Actors, Poorly Configured Technology Compound the RiskGeopolitical events increasingly pose risks to organizations’ cybersecurity posture, the current and former leaders of the U.S. Cybersecurity and Infrastructure Security Agency – Jen...